Cyber Security Risks have always been a concern for websites but in the last two years, it has become crucial. With artificial intelligence becoming more effective, the rate of sites being hacked and infected increased and there is no sign of this trend slowing down unless people start taking security seriously.
What are HTTP Security Headers?
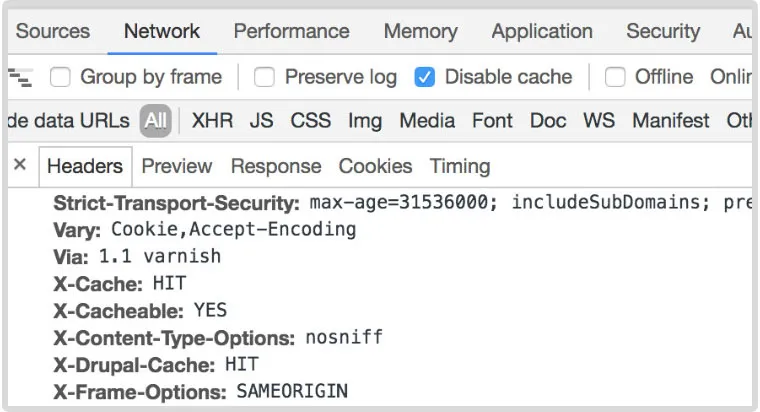
When a browser like Chrome or Safari make a request to a display a website they send that request to the server where the files reside and the server responds with the content of the website and also HTTP response headers. The response headers give information about the server and the website.
The response headers give information like: the type character encoding the site uses, status codes to tell if the site is down or has an error, what type of cache control the server uses…etc. The security headers are an important part of the security of your site because it tells browsers how to behave when handling your site. For example, enabling the Strict-Transport-Security header you can force the site to communicate over secure transport protocol(HTTPS) only. Let’s look at some of the essential security headers that are needed to keep your site secure.
Content Security Policy and Cross-Site Scripting
The content security header provides security against Cross Site scripting(XSS) attacks. These types of attacks are a type of injection, in which malicious scripts are injected into otherwise benign and trusted websites.
XSS attacks occur when an attacker uses a web application to send malicious code, generally in the form of a browser side script, to a different end user.
This attack is executed by means of input boxes on a website. A code is sent through an input box that is not validated and sanitized. This is a widespread and oft occurring type of attack.
HTTP Strict Transport Security (HSTS)
The Strict-Transport-Security tells the browser to only access the site over a secure connection. This makes sure that all data that is sent and received from the server is encrypted. To do this, an SSL certificate is needed. An SSL certificate allows data to be encrypted by using a Public/Private key pair.
X-Frame-Options
The X-Frame-Options header provides clickjacking protection by not allowing iframes to load on your website. Clickjacking is an interface-based attack in which a user is tricked into clicking on actionable content on a hidden website by clicking on some other content in a decoy website.
Here is an example of a clickjack attack. A web user accesses a decoy website (perhaps this is a link provided by an email) and clicks on a button to win a prize. Unknowingly, they have been deceived by an attacker into pressing an alternative hidden button and this results in the payment of an account on another site.
Expect-CT
The HTTP Expect-CT header is a response-type header that prevents the usage of wrongly issued certificates for a site and makes sure that they do not go unnoticed and it also allows sites to decide on reporting or enforcement of Certificate Transparency requirements.
X-Content-Type-Options
The X-Content-Type-Options header is used to protect against MIME sniffing vulnerabilities. These vulnerabilities can occur when a website allows users to upload content to a website however the user disguises a particular file type as something else. This can give them the opportunity to perform cross-site scripting and compromise the website.
Isn’t My Web Hosting Company Supposed to Protect me From Attacks?
In theory, yes, but the reality is far from ideal. We did a recent scan of 200 websites hosted on 50 different web host companies, and our results show that 96% of the scanned sites did not have security headers present. That means that most web companies are implementing security as they should.
Acunetix, a web security research company noted the following about web vulnerabilities.
46% of web applications have critical vulnerabilities
30% of web applications are vulnerable to XSS.
87% of websites have mid-level weaknesses.
This means that unfortunately that most web hosts are not doing their jobs.
Cyber Security Risks – Case Study
Recently we worked on two websites hosted with two international web hosting companies. The first site was simply switching their hosting to our secure platform Website Safeguard. When we moved it and scanned the site, we found 122 files that were hacked. There were backdoors everywhere.
Our report showed that they had been hacked for over three years and their web host had not found it nor done anything about it. After cleaning the site we were able to remove the back doors and block the IP addresses that were trying to access the back doors.
The second site was another interesting case. The site was experiencing spam being sent through a form on their site. The web host emailed their client to inform them that the site was suspended and that they needed to fix the problem. In order to fix the site it was necessary to not only upload some files but also activate the changes which required the site to be up to activate the changes.
The site was caught in a catch-22. The hosting company would not put the site up until the issue was fixed and the site could not be fixed until the site was up. The end result was that the site was down for nearly three months while the bureaucratic nightmare was resolved.
Most Web Hosting companies’ first priority is to themselves and their network.
This is the sad reality of most hosts. Their first priority is to their network. They do the minimum to protect your site. That is why they are so cheap. They do the minimum and leave the rest to you. This is a terrible model because most people that host a website are not technical people and so their web host company simply shifts the responsibility to someone that doesn’t understand technology.
If you need to help to secure your website, hosting your website, or help to program new functionality we are here to help. Our Progress Coordinators help you through all the technical details will make sure that your site is safe and secure